The BMI Difference: Security
Security Is Not A Policy; It’s A Mindset
We’re committed to the security of our people, our projects, and your data. When you choose us as your partner you can be confident that your information is handled with the care and responsibility we use to protect our own records. Below is a link to our Sunnyvale, CA headquarters virtual tour and a snapshot of some of our methods to keep your data secure.
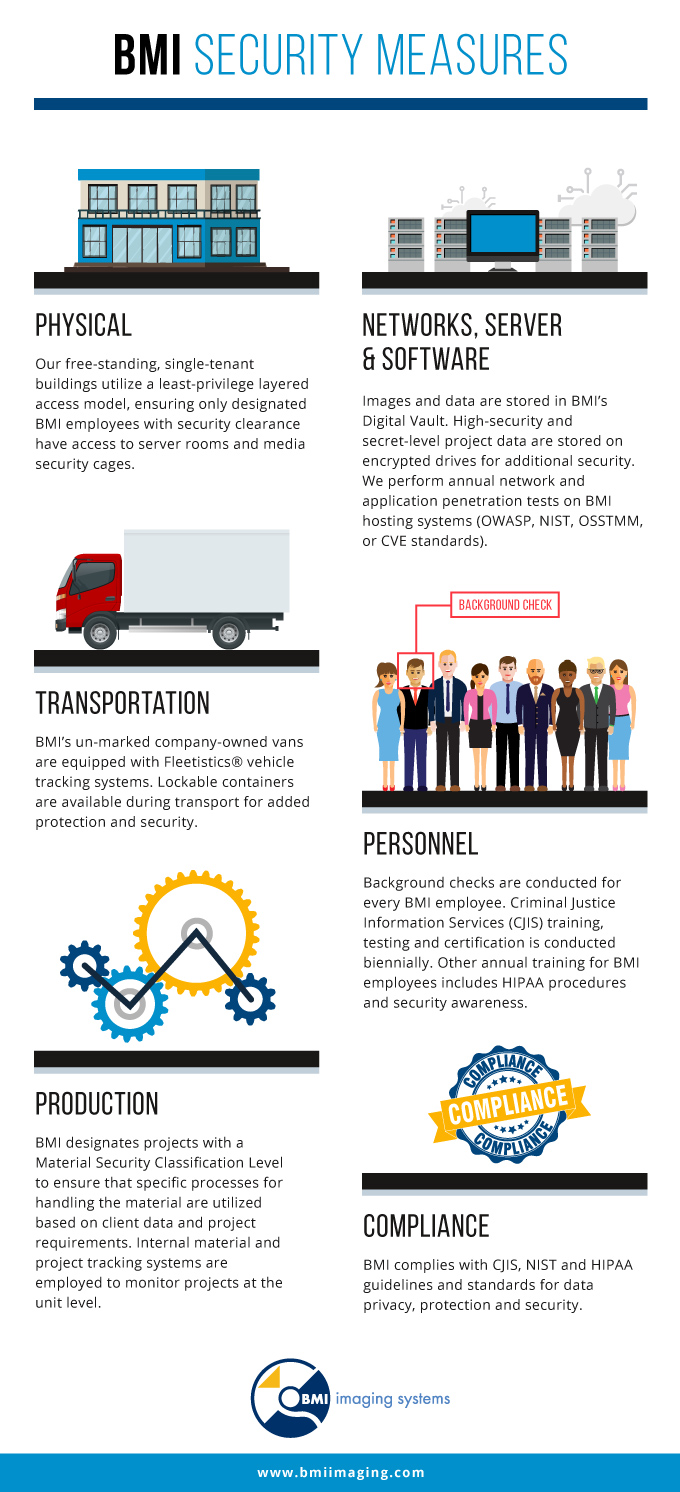
Since 1958, we’ve provided integrated document conversion and management solutions for courts, law enforcement departments, healthcare offices, labor unions, financial institutions, university registrars, and many other organizations with sensitive data. Explore and expand the drop-downs below to learn more about our methods to keep your data secure.