Does your department or agency handle, access, and process criminal justice information? Do you know what’s required of you to properly handle CJI? If you don’t know what data is considered CJI, wouldn’t you like to find out and understand what you should be doing?
If you’re one of the law enforcement agencies that deals with criminals (police department, sheriff’s office, court), then you’ll likely come across criminal justice information at some point, if not already. There are plenty of other sources to read about CJIS data, the best being the actual FBI Security Policy, but we’ve put together this article to cover some main points that you may find useful as a quick reference.
If you’re considering scanning your hard copy records into a digital format or migrating digital images from one system to another, we’ve included sections that describe different types of digital scanning projects, how to find vendors to work with, and other considerations that are important for this type of work.
It’s a decently long read so the sections are broken out to easily jump from section to section based on your most pressing topic.
What Is CJIS Digital Scanning?
When you read “CJIS digital scanning,” you’re probably thinking that it’s an industry-specific term or that if you don’t find someone that can execute a “CJIS digital scanning” project you’re out of luck. Well, the phrase isn’t part of some terminology codex; it’s something we’re using here to describe the scanning and conversion of documents that fall into the category of CJI. Before turning to the digital scanning specifics, let’s get some acronyms and definitions out of the way.
CJIS definition
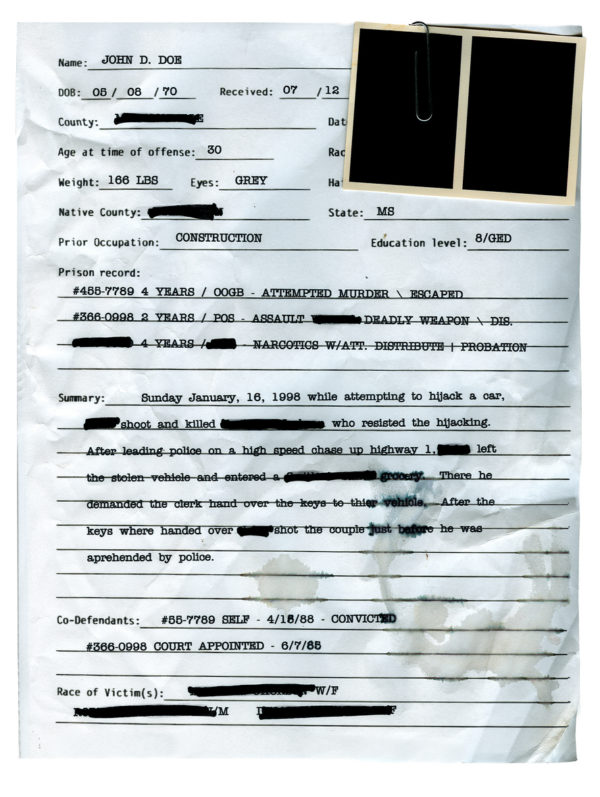
“CJIS” stands for Criminal Justice Information Services, a division of the FBI that has the mission “to equip our law enforcement, national security, and intelligence community partners with the criminal justice information they need to protect the United States while preserving civil liberties.” It’s the largest division of the FBI and it aggregates and organizes “CJI” (criminal justice information, such as criminal records and police files) so that national, state, and local law enforcement and intelligence agencies can access the information quickly and easily to protect their citizens.

How does CJIS digital scanning work?
With the background and definition of CJIS, the idea of “CJIS digital scanning” is to take hard copy records that contain CJI and scan and convert them into an electronic format.
The basic concept is pretty straightforward, but you may be asking yourself how CJIS digital scanning works in practice. We can’t speak for everyone that digitizes criminal records and documents that contain CJI, so we’re going to keep it specific to how we do things.
- First, we went through a compliance process, passed, and got ourselves placed on the CJIS vendor list.
- We also have all of our employees take CJIS certification tests so that they can work on projects that fall into the category of criminal records. According to the CJIS policies, every person in a room where CJI is being handled must have CJIS certification.
- When we move forward with a client that has CJI, we set up segregated network storage locations to keep the client’s information separate from other data. All access to these storage locations is restricted to employees that have received clearance from the agency that owns the CJI. All storage locations used for CJI are audited.
- We designate only the necessary employees that will be needed to carry out the project so we can limit the number of individuals involved in handling and processing the images and data.
- The hard copy records are stored within our facilities in locations that are separately secured from other projects; our facilities are cordoned into distinct public vs production areas, but even within the non-public areas of our facilities, we have secure sections that we can store sensitive data on an as-needed basis until the project is complete.
- Delivery of the images and data are on encrypted USB drives or through a secure FTP portal.
- If a client decides to have us host their digital content, we store their data in our secure CJIS cloud hosting environment.
What is considered CJIS data?
Now that you know more about the process of scanning your records, let’s get specific about what is actually considered CJIS data. Before we go into our own rendition of this, we’d like to provide you with the official document that you can refer to if you have any questions: the Criminal Justice Information Services (CJIS) Security Policy. This is the go-to document for any CJIS-related information, and the Executive Summary puts it nicely: “The CJIS Security Policy provides guidance for the creation, viewing, modification, transmission, dissemination, storage, and destruction of CJI.” In our view, that covers pretty much everything you’d need to know!
If you don’t feel like reading the entire CJIS security policy, though, we understand how you feel and can give you some highlights.
To quote from the Security Policy, “Criminal Justice Information is the term used to refer to all of the FBI CJIS provided data necessary for law enforcement and civil agencies to perform their missions including, but not limited to biometric, identity history, biographic, property, and case/incident history data. The following categories of CJI describe the various data sets housed by the FBI CJIS architecture:
- Biometric data – data derived from one or more intrinsic physical or behavioral traits of humans typically for the purpose of uniquely identifying individuals from within a population. Used to identify individuals, to include: fingerprints, palm prints, iris scans, and facial recognition data.
- Identity History Data – textual data that corresponds with an individual’s biometric data, providing a history of criminal and/or civil events for the identified individual.
- Biographic Data – information about individuals associated with a unique case, and not necessarily connected to identity data. Biographic data does not provide a history of an individual, only information related to a unique case.
- Property Data – information about vehicles and property associated with crime when accompanied by any personally identifiable information (PII).
- Case/Incident History – information about the history of criminal incidents.”
In addition to the above, a subset of CJI is Criminal History Record Information (CHRI), also known as “restricted data.” There are additional controls required for the access, use, and distribution of CHRI because of its sensitive nature; the proper methods are described in the Security Policy in its own section.
Some examples of CHRI include:
- Gang files
- Known or appropriately suspected terrorist files
- Identity theft files
- Violent person file
How do CJIS policies apply to digital scanning?
As we mentioned earlier, “CJIS digital scanning” isn’t really an official term that describes the specific or only way to carry out a scanning and conversion project. However, if you have files that fall under CJI and plan on having them scanned, you should know the CJIS policies that need to be implemented to properly handle the information throughout the digital conversion process.
It’s up to you and your agency to interpret and implement the policies and their requirements, but here are the thirteen listed in the “Policy and Implementation” section (Section 5) of the Security Policy, with the stated goal and subsections of each one:
The Importance Of CJIS Compliance
CJIS compliance isn’t just a fun idea that someone put together as an afterthought; you should be following the policy! If you’re not sure of what you’re supposed to be doing or if your department is implementing a method that complies with the CJIS Security Policy, you likely have a gap somewhere. The good thing is that you’re reading this article and taking the first step to getting your organization on the right track.
Why is CJIS compliance important?
Because if you want to have access to the FBI’s CJIS database, you have to follow the rules. Even if you’re not going to access the CJIS database, you should follow the Policy as a guideline of proper information handling and security procedures. If you plan to outsource some work (such as digitally scanning your records!) the third party that’s going to work with you will need to follow the same CJIS procedures, too.
What are the penalties for mishandling CJIS data exist?
Interestingly enough, there aren’t really any penalties for not following the CJIS Security Policy and handling CJI in the recommended way.
So what can happen if CJIS policies aren’t followed? You’ll probably be denied access to the database. This may not sound too extreme, but when you’re trying to put together a case or research information, not having the national database through the FBI might slow down your efforts or even prevent you from finding that critical piece of info you needed.
If you think of it like belonging to a club, you pay to play; in this case, paying is just following the Security Policy and handling, transmitting, and processing CJI in the recommended way!
Security And Storage For CJIS Digital Scanning
Now that we’ve covered the meatier topics like policies and handling requirements, let’s talk about the physical and electronic security and storage necessary for CJI-related documents.

What security measures do you need to put in place when digitally scanning CJIS documents?
Though there are many ways to implement security, we’ve put our methods and procedures in place based off of numerous projects with law enforcement agencies and researching and understanding the sensitivity of handling CJI. We’ve worked with city, county, state, and federal law enforcement agencies and believe that our security posture is well-suited for any project you have that includes criminal justice information.
If you’re interested in learning more, take a look at our “Security” page for additional details.
Types Of CJIS Digital Scanning Projects
We’ve been talking about digital scanning projects so far, and you’re most likely thinking that we’re only referring to physically scanning materials and turning them into electronic records. We are talking about those kinds of projects, and we’re also talking about digital-to-digital data migration projects.
Hard copy scanning and digital conversion
The typical scanning project includes taking paper or microfilm and microfiche records and converting them into electronic files. Hard copy to digital jobs are normally more involved than digital-to-digital jobs because of the physical handling of your material. There’s the process of packing, transporting, and maintaining a chain of custody of the original material, then creating document types and scanning; once all that’s complete, the digital processing phase begins.
With hard copy scanning projects there are usually more people involved and more hands that touch your material, just by the nature of the project. The employees who handle the digital portion of a project aren’t the same as the ones who scan the records, so it’s inherent that more people are involved.
Also, since physical material is going to be handled, there’s an additional element of security. Instead of just handling the digital data (like in a legacy data migration), there’s the physical material to deal with: this involves transportation from your facility to the scanning facility, clearing the right people who will touch your records, making sure there are physical storage locations within the scanning facility to properly contain the criminal justice information, and keeping the records separated from other projects that don’t require a security posture such as that of CJIS-type data.
Legacy data conversion and migration / digital-to-digital
Here’s a simple way to describe this type of project: you have electronic files in an old application and you want them moved to a new records management system. A legacy data migration is the method of getting your files from one system to another.
Instead of going into heavy detail here, we recommend you take a look at our article that explores legacy data migrations in detail. Once you know the process for a data conversion and migration project, all you have to do is apply CJIS specifics and you’re off to the races!
What equipment do you need to digitally scan, access, and store CJIS data?
Nothing special, really. It’s not the equipment itself that allows you to scan CJI (or access or store) but rather the methods you create and implement to protect the data. As the old saying goes, “it’s not the clubs; it’s the golfer!”
If you’re thinking about getting some scanner to convert your hard copy files just keep in mind that it’s the security surrounding the scanning that’s most important, not necessarily the actual machines. The same goes for the systems you use to access and store the data – make sure the document management system has access privilege capabilities, audit tracking, and so on. For physical storage, ensure you keep CJI properly segregated so that only authorized personnel can get access to the files.
On another note, if you’re thinking about doing your own scanning from hard copy to digital then we suggest you take a look at our article “Why Should I Hire A Scanning ‘Expert?’” In the article we give some ideas about what it takes to do your own scanning and why you may want to consider outsourcing the work to someone like us (semi-shameless plug for our services!). Scanning is sometimes overwhelming for agencies that aren’t focused on this type of work, and if you have to stop doing your real job to hop on a scanner and convert a storage room of boxes of thousands of microfilm rolls, you could probably be spending your time more effectively. Let us (or someone like us) do the dirty work for you!
CJIS Digital Scanning Vendors
Okay, we’ve gone over a lot of information so far and by now you’re probably thinking “great, I get it, CJIS is important! But who can I work with??”
The simplest way to find a vendor who’s capable of processing CJIS data is to go to the CJIS directory and search! If you’ve already been talking with a couple of companies about your scanning project, check them against the CJIS-listed vendors; if they’re not listed, then you’re probably not going to want to send them your criminal data.
How does a digital scanning vendor become CJIS compliant?
Saying “CJIS compliant” is a bit of a misnomer because most of the companies that scan CJI data don’t actually have to be compliant. It’s YOU, the law enforcement agency, that must be compliant, not the scanning or data processing vendor.
You’re looking for a company that is a CJIS-listed vendor and has the proper methods and procedures in place to handle your criminal data, not actually be compliant in the sense of the FBI CJIS Security Policy.
What should you look for in a CJIS-compliant digital scanning vendor?
First, make sure the company that you’re going to work with is a CJIS-listed vendor by checking out the website that lists companies authorized to handle CJI. If they’re listed, you should be comfortable that they have the requisite procedures in place to process CJI and have been vetted by the proper authorities.
Next, compare the ways in which the companies run their projects. Assuming you’re comparing a couple of companies that you found listed on the CJIS portal, they’re both vetted and approved to handle CJI, but that doesn’t mean they do things the exact same way. You may like the processes of one over the other, and you’ll have to do your research by talking to both and asking detailed questions about their project process. We recommend that you tour their production facility(ies), if possible, and ask for a copy of their most recent security audit results. Also ask for references from other agencies they’ve worked with on similar projects.
Don’t forget price! Price isn’t everything, but it sure counts for quite a bit, right? Every company will price their services differently, so get into the weeds about how your CJI project will be structured and make sure you’re getting what you need without a bunch of hidden fees. Something to note about pricing and fees that we mention in another of our articles:
- don’t expect the lowest priced vendor to get you what you really want! You pay for what you get.
- on the flipside, don’t expect the highest priced vendor to be the best. Anyone can pretend to be awesome just by pricing themselves high, but that doesn’t directly translate to successful outcomes.
Our recommendation is to do your research, ask vendors a lot of questions about how they do what they do, and make sure you feel comfortable about all aspects of your project before signing a check.
Where do you find digital scanning vendors that are CJIS compliant?
If you’re just starting your research for a scanning project, go to the CJIS online portal and begin there.
If you’re already chatting with a company or two and want to check to see if they’re capable of handling your data, visit the same link and cross-check them to make sure they’re listed. If they’re not listed in the portal, you may want to look for an alternative.
What Types Of Records Can Contain CJI?
Short answer: any type.
Paper, microfilm, born-digital; all of these types (formats) can contain CJI.
Another way to interpret the term “types” is based on the actual content of the material, not necessarily the format. To answer this question you can go to section 4.1 Criminal Justice Information in the Security Policy to read about the specific content types that contain CJI. This info is also in this article under the section “What is considered CJIS data?”
Next Steps
Reach out to us today! Click the “Get Your Quote” button below, fill out the form, and we’ll quickly reply to you to discuss your project.
Further Reading
Below are some other articles and pages we’ve put together to give you some more information about our services.
“The BMI Project Review Process” illustrates our step-by-step approach to take your digital conversion project from idea to reality. If you want to know how we do what we do and what you can expect from us, this is a great place to start.
“Legacy Data Migration” goes over how to transfer (“migrate”) your data from an old system to a new one. Technology changes and companies come and go, so if you have images and data stuck in a legacy system and want to move it to a new one, this article’s for you.
“Traditional Microfilm Conversion vs. Digital ReeL” is a comparison of what we call a “traditional” method of scanning film (creating PDFs, TIFs, etc.) and our Digital ReeL solution. There isn’t a right or wrong way, so if you’re not sure what options you have available to you and are curious about the pros and cons, this is a good place to start.
“Microfilm Deterioration: How To Identify It And How To Preserve Your Content” illustrates a few examples of ways your film can decay over time and how to prevent losing your film’s content forever. Yes, we’ve had clients with microfilm so bad that we had to clean our scanners after every roll; some rolls couldn’t even be scanned they were so far gone!

